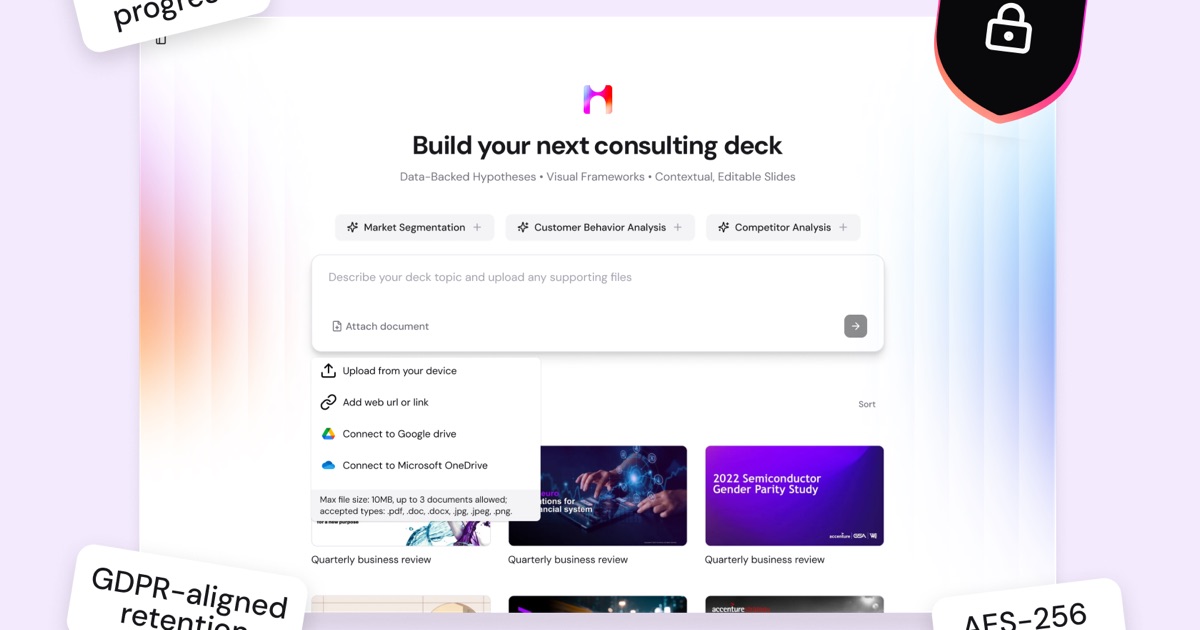
TLDR: Enterprise AI presentation tools handle sensitive corporate content including strategy decks, financial projections, and competitive intelligence. This checklist covers SOC 2, GDPR, EU AI Act, and data residency requirements so procurement and legal teams can evaluate vendors systematically.
Why AI Presentation Security Matters for Enterprise
Enterprise presentation tools handle sensitive corporate content including strategy decks, financial projections, and competitive intelligence. According to IBM’s 2024 Cost of a Data Breach Report, “the global average cost of a data breach reached $4.88 million” with even higher figures for regulated industries.
The Compliance Landscape
SOC 2 Type II
SOC 2 Type II tests operational effectiveness over 6-12 months. It covers security, availability, processing integrity, confidentiality, and privacy. The certification validates access controls, encryption, incident response, and change management.
GDPR and Article 22
GDPR applies to tools processing personal data of EU residents. Article 22 requires human oversight for automated decision-making. It mandates data processing agreements and subject access procedures.
EU AI Act
The EU AI Act entered force August 1, 2024. The enforcement timeline includes: prohibited practices (February 2025), general-purpose obligations (August 2025), and high-risk systems (later 2025). Penalties reach “up to 35 million euros or 7% of global annual turnover.”
Data Handling: Where Your Content Goes
Critical considerations include:
- Model training policies and contractual commitments
- Data residency requirements
- Retention and deletion timelines
- External processor chains
- Encryption standards (AES-256 minimum)
Vendor Evaluation Checklist
Certifications and Compliance
- SOC 2 Type II (not Type I)
- GDPR documentation with Data Processing Agreement
- ISO 27001 certification
- EU AI Act readiness assessment
- NIST AI Risk Management Framework alignment
Data Handling
- No training on customer data
- Data residency options available
- AES-256 encryption at rest, TLS 1.2+ in transit
- Clear retention/deletion policies
- Published processor list
Access Controls
- SSO via SAML 2.0 or OIDC
- Role-based access control with granular permissions
- SCIM provisioning
- Accessible audit logs
- Mandatory MFA
Incident Response
- Documented response plan with defined SLAs
- 72-hour breach notification (GDPR aligned)
- Regular third-party penetration testing
- Vulnerability disclosure program
Deployment Options
- Cloud with dedicated tenancy option
- Private or on-premises deployment
- API access controls and rate limiting
- Data export capabilities
Critical Questions for Vendors
- Which systems process content, in which jurisdictions, and for how long is it retained?
- Can you contractually guarantee data won’t be used for model training?
- Provide complete processor list including inference providers and analytics services.
- Describe your last security incident and remediation timeline.
- What’s your compliance roadmap for the EU AI Act’s high-risk system rules?
- What infrastructure isolation guarantees exist between tenants?